-
روغن موتور بی ام و 5w-30
۱,۰۵۰,۰۰۰ تومان -
روغن موتور موبیل وان Mobil 1 سیلور آمریکا
۱,۰۰۰,۰۰۰ تومان -
شمع ولوو XC90 سال های 2016 تا 2017 – 31673604
۱,۵۰۰,۰۰۰ تومان -
شمع پورشه پانامرا و کاین – 99917013090
۹۵۰,۰۰۰ تومان–۱,۵۰۰,۰۰۰ تومان -
لامپ زنون D1S فیلیپس – 85415VIC1
۱,۸۱۰,۰۰۰ تومان -
کوئل بی ام و سال های 2009 تا 2017 – 12138657273
۱,۵۰۰,۰۰۰ تومان -
شمع بی ام و موتور N52 سال های 2004 تا 2015 – 12122158253
۲۴۰,۰۰۰ تومان -
پیچ چرخ بی ام و سال های 2007 تا 2019 – 36136781151
۴۰۰,۰۰۰ تومان -
اکتان بنزین مرسدس بنز – A0009892545
۱۳۰,۰۰۰ تومان -
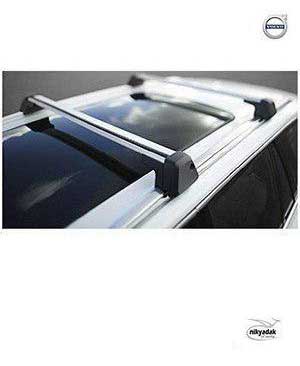
باربند سقف ولوو XC90 سال های 2016 تا 2017 – 31373449
۳۸,۰۱۰,۰۰۰ تومان
-
دنده ونوس پورشه پانامرا و کاین سال های 2012 تا 2015 – 94810505123
۶۳,۰۰۰,۰۰۰ تومان -
کاسه نمد دیفرانسیل ولوو XC90 سال های 2014 تا 2017 – 30735124
۲,۲۵۰,۰۰۰ تومان -
کاسه نمد دیفرانسیل ولوو XC60 سال های 2014 تا 2017 – 31256727
۲,۸۰۰,۰۰۰ تومان -
کاسه نمد ته میل لنگ ولوو XC60 سال های 2013 تا 2017 – 8694809
۷,۸۰۰,۰۰۰ تومان -
کاسه نمد ته میل لنگ ولوو V40 سال های 2013 تا 2017 – 9458178
۲,۷۰۰,۰۰۰ تومان -
کاسه نمد ته میل لنگ ولوو XC90 سال های 2017 تا 2019 – 31480636
۲,۷۰۰,۰۰۰ تومان -
واشر درب سوپاپ ولوو XC60 سال های 2014 تا 2017 – 31359965
۴,۵۵۰,۰۰۰ تومان -
شمع موتور ولوو XC60 سال های 2014 تا 2017 – 30758130
۱,۵۰۰,۰۰۰ تومان -
فیلتر هوا ولوو V40 سال های 2013 تا 2017 – 30757155
۱,۰۵۰,۰۰۰ تومان -
لنت ترمز جلو ولوو V40 سال های 2013 تا 2017 – 30742029
۸,۳۰۰,۰۰۰ تومان -
بوش رام جلو پورشه کاین سال های 2007 تا 2015 – 95534113301
۳,۲۵۰,۰۰۰ تومان -
لاستیک چاکدار پورشه پانامرا سال های 2012 تا 2014 – 97034379205
۴,۳۰۰,۰۰۰ تومان